There are affiliate links on this page.
Read our disclosure policy to learn more.
Drink More Water popups on your Android (Samsung Galaxy, LG, Motorola, etc.) cellphone?
Are you getting "Drink More Water" popups on your Android (Samsung Galaxy, LG, Motorola, etc.) cellphone?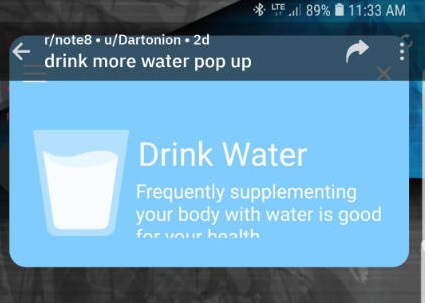
Are you getting popups on your Android cellphone like
-
"drink more water" or
-
"optimizing my battery" or
-
"device running hot" or
-
" battery temperature is too high".
And when they popup none of your phone controls do not work, so you must wait until the popup ad finishes loading and you can click the X in the corner of the ad?
It's spam malware.
What to do:
A present it appears as though NOTHING works except to do a factory reset on the phone.
We just tested the free 30 day trial of Malwarebytes (download it from the Google Play Store here). Unfortunately, MalWareBytes did not find it nor remove it. Only a factory reset works.
Anti-virus programs
Norton anti-virus does not appear to be able to remove it.
Recommendations
Unfortunately, the only proven solution appears to be to do a factory reset on your phone.
And that is annoying because you will have to download apps again and set up your email accounts all over.
How to do a Factory Reset
Samsung provides detailed instructions on how to do a factory reset on this page. Below are quick steps:
- Save any information you need prior to the factory reset because your personal information may not be recovered.
If you have encrypted the microSD card, you must decrypt it before resetting the phone. Otherwise, your phone will not be able to read the data on the card. From Settings, search for and select Decrypt SD card, and then follow the on-screen prompts. - Make a list - on paper - of all the apps which are not standard - that you use. You will need to reinstall them after the reset.
- From Settings, search for and select Factory data reset.
- Tap Factory data reset again, and then review the information.
- When you're ready, swipe to and tap Reset.
- Next you will need to reinstall apps that you use.
Definitions: What are viruses, Trojans, worms and more?
Malware is a category of malicious software code that includes viruses, worms, bots, backdoors and Trojan horses. Malware uses popular communication tools to spread, including viruses and worms that are sent through email and instant messages, Trojan horses in email attachments or received when you visit a corrupted website, and virus-infected files downloaded from file sharing P2P connections. This can be confusing, so here is a simple breakdown. See this article from CISCO for a more detailed description.
Viruses
A computer virus propagates itself by inserting a copy of itself onto your computer. Viruses can range in severity from causing mildly annoying effects to damaging data files or software. Almost all viruses are attached to an executable file, which means the virus may be on your computer or in an email, but will not be active or able to spread until you run it, click on it, or open the file or attachment.
Worms
Computer worms are similar to viruses in that they reproduce copies of themselves and can cause the similar damage. But worms are standalone software and do not require the user to open an attachment (although they can) - often they take advantage of weaknesses in operating systems to spread from computer to computer throughout a network (home or company)
Trojans
A Trojan is named after the wooden horse the Greeks used to enter Troy. It is a harmful file that looks legitimate, such as "Attached is your invoice. Click here to open it.". Users are typically tricked into loading and executing it on their systems. After it is activated, it can achieve any number of attacks on the host, from irritating the user (popping up windows or changing desktops) to damaging the host (deleting files, stealing data, or activating and spreading other malware, such as viruses). Trojans are also known to create back doors to give malicious users access to the system.
Bots
"Bot" comes from the word "robot" and is an automated process that interacts with other network services. A typical good use of bots is to gather information (such as web crawlers), or interact automatically with instant messaging (IM), Internet Relay Chat (IRC), or other web interfaces. They may also be used to interact dynamically with websites. Bots can be used for either good or malicious intent. A malicious bot is self-propagating malware designed to infect a host and connect back to a central server that may control an entire network of compromised devices, or "botnet. Bots can include the ability to log keystrokes, gather passwords, capture and analyze packets, gather financial information, launch DoS attacks, relay spam, and open back doors on the infected host.
Backdoor
A back door is an undocumented way of getting into a computer system, bypassing the normal security logon mechanisms. Some back doors are placed in the software by the original programmer and others are placed on systems through a system compromise, such as a virus or worm. Usually, attackers use back doors for easier and continued access to a system after it has been compromised. This is common when software makes your computer a "zombie".
For a comprehensive list of national and international agencies to report scams, see this page.